It’s never too early (or late) to learn about keeping your loved ones safe online. Good online habits such as critical thinking, responsible behaviour, and honest communication can help avoid tough situations. Anyone can fall victim to a social engineering attack or security breach, so protect your less tech-savvy family members with these great tips!
Family impersonation scams
The ACCC recently published an article about text message scams where the sender pretends to be a child of the person they’re contacting.
“The scammer will claim they have lost or damaged their phone and are making contact from a new number. Then, once they have developed a rapport with their target, the scammer will ask for personal information such as photos for their social media profile or money to help urgently pay a bill, contractor or replace the phone.”
If you receive one of these messages, try calling the number you already have saved for the family member, or some secondary contact method. If they respond you know the message was a scam.
Family computer security
Health IT offers security for your home computer! Often we find that a simple antivirus isn’t enough to combat malicious actors online. Health IT Home Security as a unique, affordable offering that brings layered, business class security to your home computers, without taking a heavy handed or restrictive approach.
Read our release article for more info, or Click here to enquire about Health IT Home Security
Many people think they’re simply not valuable enough to be targeted by hackers, but in reality everyone is a viable target and everyone has something that can be leveraged.
The most common password in the world is ‘123456’, with ‘password’ and ‘111111’ not far behind. Change your default passwords!
Put wireless devices on a Guest WiFi network
Smart Home devices and Internet of Things (IoT) devices are a major target for hackers. In 2021, the amount of hacked IoT devices was in the billions, and that number is steadily climbing. Often these devices don’t have the same security as your computer or phone, and can provide an entry point to your home network for some enterprising criminal. ‘Smart’ Devices like speakers, fridges, and lightbulbs might seem innocent and fun to many technophiles, but they all come with associated risks.
Because of this, it’s recommended to connect any ‘at risk’ devices to a separate network in your home, that doesn’t have a direct connection to your computers. It’s also worth checking if these devices have a default admin password like ‘12345’ or ‘admin’ which should be updated.
How to create a second WiFi network
Creating a Guest network can vary wildly between routers, so here’s some basic steps, which may not apply to everyone:
- Log into your internet router from a web browser.
- Navigate to the ‘WiFi’ section to see your current network/s.
- Find the option to enable Guest network and click on it.
- Set a strong password (often called WPA key) for the network.
- Set a new password for your main WiFi network also. This will disconnect all currently connected IoT devices.
- You may need to reboot your router.
If the above steps do not work, or you’re unsure what to do, find the brand/model written on the router and search for an instruction manual online. The manufacturer will hopefully have detailed instructions to set up a guest WiFi network.
Once the Guest network is set up, go into settings on the smart device and choose to connect to a new WiFi network. The connection you just set up should appear in the list to select. Reconnect your sensitive devices (computers, phones etc.) to the main network.
Identify 'safe websites' when shopping online
There’s a significant overlap between scarily-accurate advertising algorithms and the lowered defences of shopping online at home that makes us perfect targets credit card scams and identity theft. If you see something advertised on Facebook or Instagram, instead of clicking directly through the ad, do a Google Search for the brand company or item name and find the item that way. Often people can use ads that direct to fake business pages to steal your data, thinking you’re buying from the real supplier.
If you’re entering credit card or shipping details anywhere on the web, make sure the site you’re using has an encrypted connection. To check this, look for the closed padlock icon next to the web address.
If you don’t see a padlock, or if you get a warning before entering the website, be safe rather than sorry – Do not enter any personal details, especially not financial info.
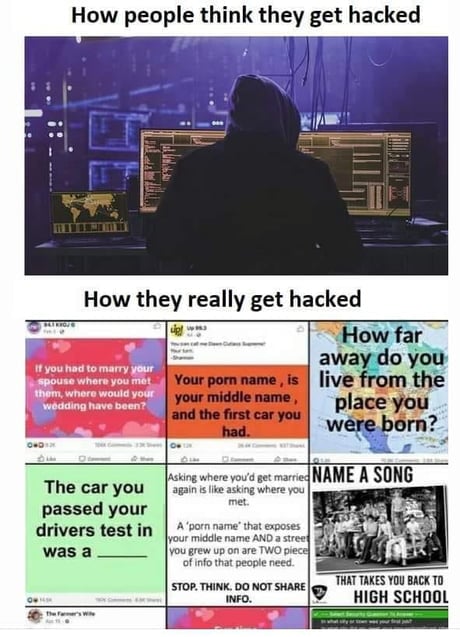
Be aware of Social Media quiz scams
Social Media is a fantastic target for scammers to gather all kinds of information on their targets, and their attempts are getting harder to spot.
A seemingly harmless quiz could trick you into giving up your date of birth, the street you grew up on, a pet’s name, or your mother’s maiden name – All potential passwords or secrets to gain access to your accounts.
Be very wary of posts asking for your favourite colour, food, sports team, first car or first job. These are common account recovery questions used for all kinds of online services, not just social media.
Emails from yourself or family members
A popular trick scammers love is to use a tool or piece of code that makes it look like their emails are coming from whatever address they’re sending to. These can be disarming at first glance, but will usually be a vague threat trying to get you to send them money as ransom or get you to visit a link. Often scammers will brag about being ‘untraceable’ but this is a flimsy attempt to make you doubt yourself.
Keep in mind thousands of these are being sent out all the time to random addresses, and are likely not targeting you directly. Ask your friends or other family members if they’ve ever got a similar message and you’ll see just how many people get them.
Factory reset devices before selling or throwing out.
Selling a smart watch online, or throwing away an old modem? Any information it collected about you during your time together could be available to whoever gets their hands on the device. Because of this, you’ll need to be responsible and take steps to wipe yourself from its memory, especially if it had access to your home network or any personal details.
For things like phones and tablet PCs, often these devices hold way more data than you expect about you and your habits online. Always consult the manufacturer’s instructions to wipe user logins and factory reset them.
Resources
Health IT provides free online security training to our clients and safety resources for download from our website.
To ensure your staff are keeping patient data secure, arrange a security audit by getting in touch today.
For more info and articles, visit our Tech Blog.
5 Ways hackers target your mobile devices
5 Ways hackers target your mobile devices For more tips and how-to’s, visit our tech blog Smartphones and tablets...
Security For Your Home Computer
Introducing Health IT Home Security For more tips and how-to’s, visit our tech blog You keep your practice...


