Security Update September 2022 For more tips and how-to’s, visit our tech blog Optus Breach You may have seen in the news that Optus were the victims of a serious data breach over the last few days. This continues a trend of personal information being stolen and we expect to see…
Search Results for:
Introducing Health IT Home Security For more tips and how-to’s, visit our tech blog You keep your practice as secure as possible, but what about your home computers?Many of you have asked us what we recommend for your home computers, and we have not had a clear solution for you…
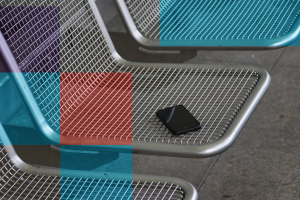
What to do when your mobile device is missing or stolen For more tips and how-to’s, visit our tech blog Whether you’ve lost a phone in an Uber or need to find a missing laptop, few things invoke instant panic like our favourite and most vital technology going missing. These devices…
Get More laptop time with these Battery saving tips For more tips and how-to’s, visit our tech blog One of the big draws of a laptop computer is that you can use it anywhere. You don’t need to have it plugged in all the time because it has an internal…
Book Your Free Practice Health Checkup For more tips and how-to’s, visit our tech blog We are thrilled to offer a new Practice Health Checkup with our Practice Liaison Officer – Adrienne.A Practice Health Checkup is the perfect chance to discuss:The general health of your IT systems;Where your business is…
Was Medicare Web Services a rough journey for your clinic? Health IT can help your practice run smoother Our decades of experience supporting practices just like yours gives us the skills to manage your IT efficiently. We have the knowledge to plan, support, and care for your practice during even…
Health IT helps you take the pain away Are you starting a new Medical Practice? Whether you’re looking to open a practice in the GP, specialist, dental or allied health field, Health IT are a one stop shop that can take care of the planning and set-up of all your…
Should You Shut Down Your Computer Every Day? For more tips and how-to’s, visit our tech blog Does Shutting Down or Restarting your computer every day help performance? While every machine will be slightly different, there are things you can do to help your computer last longer. Often software manufacturers…
Should You Upgrade To Windows 11? For more tips and how-to’s, visit our tech blog Windows 11 launched on 5th October 2021 and has steadily been patched and installed on a wider number of computers. If you’ve bought a new laptop or desktop recently it will likely come pre-loaded with…
5 Ways hackers target your mobile devices For more tips and how-to’s, visit our tech blog Smartphones and tablets are often the preferred device for communications, web searching, and accessing many types of apps. They’re more portable and can be used from anywhere. We’re seeing the takeover of many activities that…